WHAT IS ETSI EN 303 645 STANDARD?
ETSI EN 303 645 is a standard developed by the European Telecommunications Standards Institute; [ETSI], which is one of the three ESOs (European Standards Organization) with CEN and CENELEC which are recognized as European Standards (ENs).
ETSI EN 303 645 is a standard that brings together baseline requirements regarding cyber security for consumer IoT.
ETSI EN 303 645 CONSULTING PROCESS
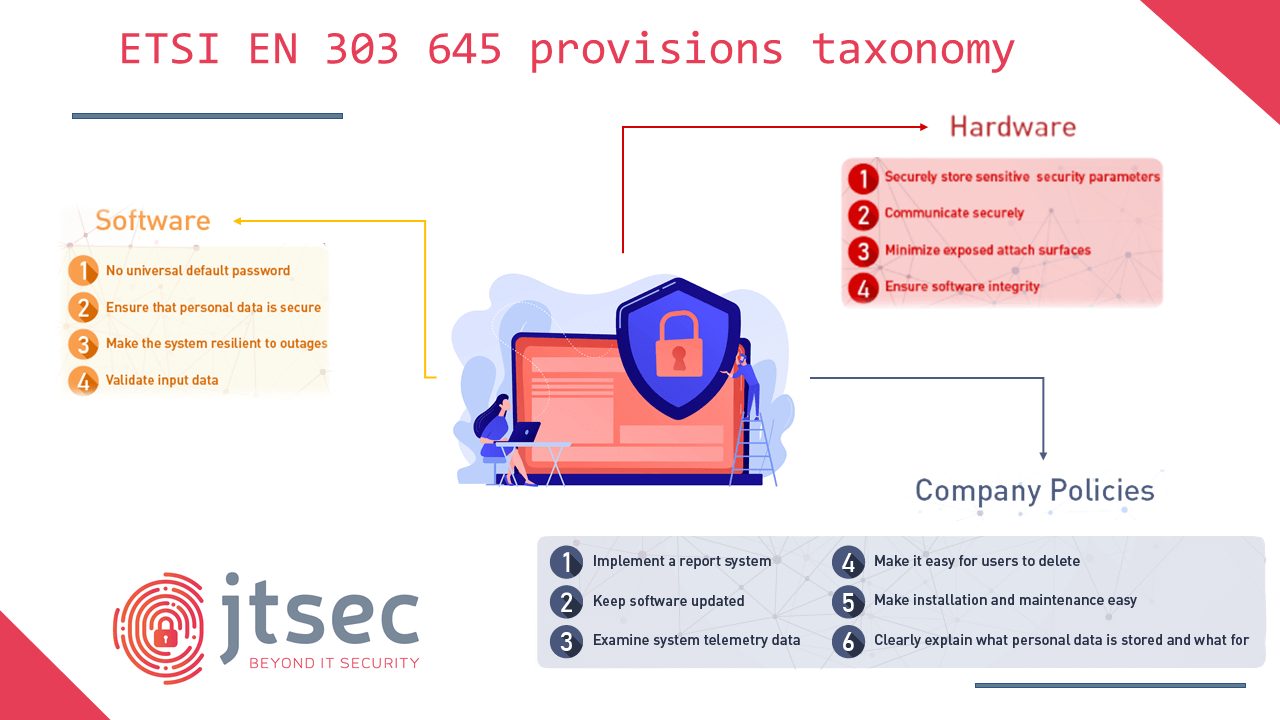
The ETSI EN 303 645 security standard aims to ensure that consumer IoT devices are protected against the most common cybersecurity threats. To this end, it contains a set of security and privacy requirements and recommendations that manufacturers should implement in their products. These specifications cover different areas and are divided into 14 categories and 67 provisions, regarding both hardware and software design, but also some company policies concerning the user data management and design principles. Find here the complete table.
The consultancy phase is mainly based on drafting the SO Statement. This Statement is a document that includes the identification of the DUT (Device Under Test), the creation of the Implementation Conformance Statement (ICS) and the Implementation Extra Information for Testing (IXIT).
- DUT (Device Under Test): The Device Under Test (DUT) is a specific consumer IoT device which is subject to assessment against the provisions of ETSI TS 103 645 / ETSI EN 303 645.
- Implementation Conformance Statement (ICS): statement, made by the SO, of the capabilities implemented in or supported by the DUT.
- Implementation eXtra Information for Testing (IXIT): record which contains or references all of the information (in addition to that given in the ICS) related to the DUT and its assessment environment, which will enable the Test Laboratory (TL) to perform appropriate test activities.

10 REASONS FOR CHOOSING JTSEC
- We assure you a fixed price from the beginning, avoid surprises!
- Time to market, a support engineer is always available for projects, ensuring we meet deadlines and expectations.
- Members of SCCG (Stakeholder Cybersecurity Certification Group).
- First ETSI accredited laboratory.
- Customized approach adapted to your needs.
- More than 15 years of experience in cybersecurity evaluation and consultancy.
- Continuous in-house training to be always up to date with regulations.
- ECSO members in the Working Group "Standardization, Certification and Supply Chain Management".
- We collaborate in different standardization projects, being ISO members, editor at JTC13 WG3 in different standardization projects.
- Accredited lab for Common Criteria, IEC 62443 4-1, IEC 62443 4-2 & LINCE.
WHAT DO WE OFFER?
-
1. GAP ANALYSIS
We assess the current status of your product and its documentation, informing you about the changes you need to make before proceeding with the evaluation process.
This service is very interesting, as specific requirements must be met and understood clearly, avoiding problems in the later stages of the development process.
-
2. CONSUMER IOT CIBERSECURITY CONSULTANCY
Drafting the necessary documentation in a timely manner is a difficult task. We provide comprehensive support to help you comply with ETSI EN 303 645 standard.
With this service we will generate all the necessary documentation and assist you in the development of both the life cycle of your product and the component itself, saving you time, money and resources.
Evaluating under ETSI EN 303 645 can be a significant challenge for a manufacturer, jtsec assists you throughout the process to meet your security objectives. This service can include gap analysis, the identification of the DUT (Device Under Test), the creation of the Implementation Conformance Statement (ICS) and the Implementation Extra Information for Testing (IXIT).
-
3. TRAINING
If you need your team to learn more about consumer IoT cyber security, we have provided many clients with customized training sessions, tailored to different levels and durations. Our training days often include hands-on workshops if required by the client.