WHAT IS EUCC
EUCC will be the first scheme published under the guidelines of the CSA (Cybersecurity Act), which proposes the creation of a common European framework for the certification of "cybersecure" ICT products and services. It can be considered a horizontal scheme, as it can be usable in several sectorial competences. EUCC is based on Common Criteria (ISO/IEC 15408 and ISO/IEC 18045) and is aimed at replacing the current national certification schemes also based on Common Criteria. It is therefore commonly known as the European Common Criteria, EUCC has recognition & acceptance only in the EU The existence of cybersecurity schemes recognized by the European Commission provides a framework in which cybersecurity laboratories, private companies and public administrations can abide when certifying their products within Europe, in the case of the EUCC, for ICT products.
*Disclaimer: Because the EUCC scheme has not yet been officially approved and published, assessments cannot be carried out.
EUCC TIMELINE AND ADAPTATION
Although EUCC is still awaiting its final version to be officially published, it is expected that the standard will be fully operational in 2022. Based on the discussions with the European Commission, the scenario of a "big bang" has been considered as the most probable one, being it consists of the following: All existing schemes cease at the same date. There is zero parallel emission of EUCC and SOG-IS MRA certificates for the same ICT products during the transition period. To minimize this impact, ENISA is creating transition guides that will allow laboratories and manufacturers to adapt to the new conditions. There will be a transition period, however, which will allow: Termination of current certification projects under the existing schemes, or their easy conversion into EUCC projects. Smooth transfer of certificates that require maintenance in the long run, therefore under for the EUCC scheme, or reuse for composite evaluations and certifications under the EUCC scheme. If you want to know more about the process followed by the EUCC until it was approved by the European Commission, please read the post in our blog called:
ENISA publishes EUCC 1.1.1 the first European cybersecurity scheme for ICT products.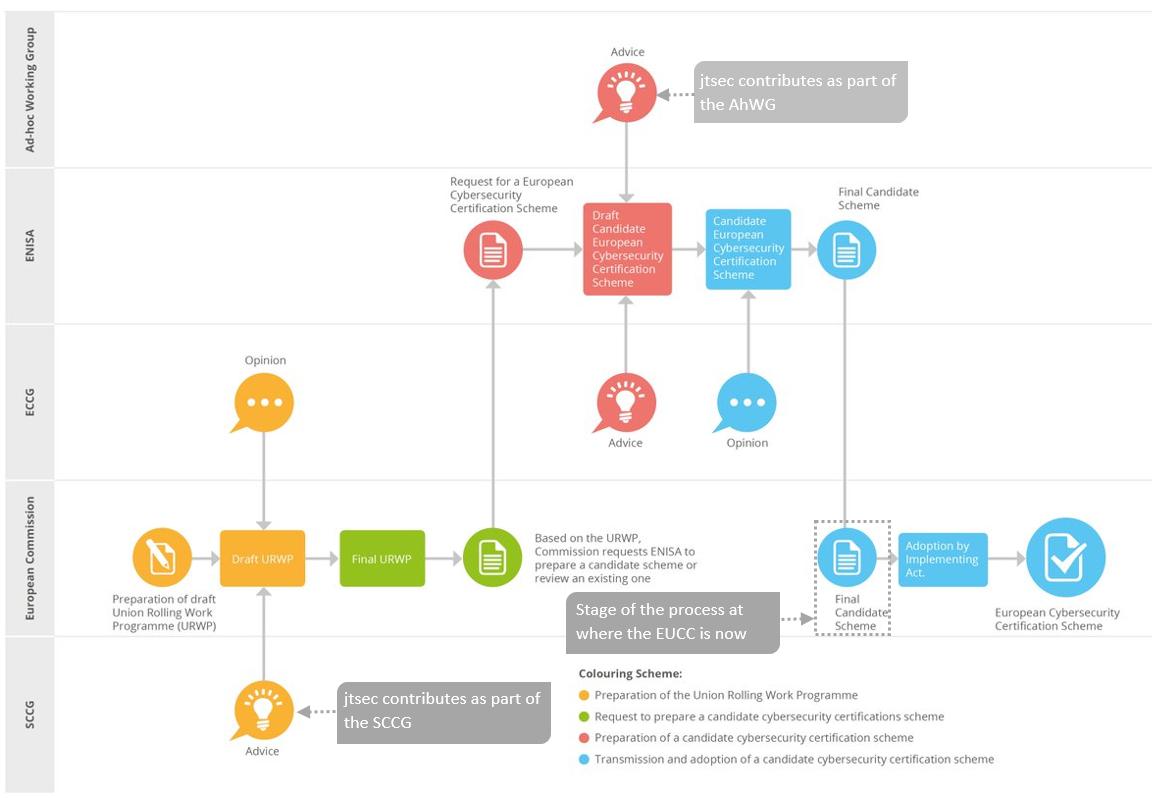
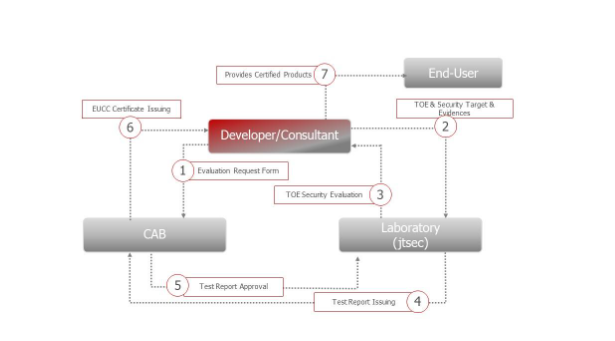
HOW TO OBTAIN A EUCC CERTIFICATION?
To obtain EUCC certification, the product must be evaluated by a laboratory that acts as a reliable and technically trained third party. The laboratory will review the manufacturer´s documentation and perform tests to verify that the product conforms to its specification. The manufacturer of the product delivers to the laboratory the Security Target (ST), which defines the scope of certification, guidelines for use and safe configuration of the product. In addition, it will use information from public sources, such as technical specifications or product data sheets. With this documentation, the laboratory will obtain the information necessary to perform a series of tests to try to identify and exploit product failures and vulnerabilities. On the other hand, the evaluation may also include testing of the cryptographic components and analysis of the source code. The results of the laboratory evaluation are reflected in an Evaluation Technical Report (ETR), which the CAB will review and, in the event that the evaluation has not found any security faults or nonconformities, issue the EUCC certificate, which certifies that the product has been satisfactorily evaluated.
10 REASONS FOR CHOOSING JTSEC
1. Top notch experts. 2. Customized approach. 3. Laboratory accredited for Common Criteria assessments. 4. Members of the SCCG (Stakeholder Cybersecurity Certification Group). 5. We use unique tools developed by us that save up to 50% of time and money in the evaluation. 6. We assure you a fixed price from the beginning, do not face unexpected surprises! 7. Deliver on time on launch a support engineer is always available for projects, ensuring we meet deadlines and expectations. 8. Editors at JTC13 WG3: “Cybersecurity Evaluation Methodology for ICT products. 9. Members of the EUCC Ad Hoc Working Group on the SOG-IS successor scheme. 10. Commitment to your project before, during and after certification.