
Our extensive experience as experts allows us to know what are the most frequent doubts in the field of cybersecurity certification, there are many people who ask us certain questions that we have considered necessary to group by assessment methodologies.
We hope that the following questions and specific answers will help to clarify doubts. If you don’t find what you are looking for, you can also write your question in this form and we will try to answer as soon as possible.
Common Criteria Frequent Questions
How to choose EAL in Common Criteria?
Selecting an EAL (Evaluation Assurance Level) is not an easy task. Depending which assurance level you want to comply, there are 7 EALs defined, the higher the number, the higher the effort to pass the evaluation. According to our Common Criteria Statistics Report, the most demanded EALs are 2, 4 and 5. If you want to know more about the requirements requested for each EAL, check our Common Criteria cheat sheet. At the end, the decision should be driven by your market target and the maturity of your development processes.
How long does it take to obtain a Common Criteria certification?
Depending on the EAL/PP against the product is being tested, the higher the assurance level is, the longer it usually takes the certification to be carried out. As a basic guideline, a Common Criteria certification needs around 6-8 months to be completed, then there are many factors that can make the consultancy or evaluation process take longer (serious vulnerabilities found, errors and inconsistencies in the product documentation...).
How much is a Common Criteria certification?
The budget needed to face a Common Criteria certification will depend on the EAL/PP chosen to evaluate the product and the scope of the evaluation. The higher assurance level, the higher cost of the certification. At jtsec, we adjust the budget for each client once we have analyzed the project, with the idea of offering the most suitable approach.
In which countries can I obtain the Common Criteria certificate?
There are two types of Common Criteria member countries, those that are authorized members (countries with laboratories and certification bodies able to assess Common Criteria) and those that are consuming members (countries that do not assess, but do recognize Common Criteria certification).
Authorized members: Canada, France, USA, Italy, Spain, The Netherlands, Germany, Sweden, Australia, India, Japan, Malaysia, New Zealand, Norway, South Korea, Singapore and Turkey.
Consuming members: Austria, Czech Republic, Denmark, Ethiopia, Finland, Greece, Hungary, Poland, Israel, Pakistan, Indonesia, Qatar, UK and Slovak Republic.
How to start a Common Criteria certification?
Certifying a product under the Common Criteria standard is not a simple process, so we recommend that the first step is to carry out a Gap Analysis. The first decisions to make are: assurance level you want to achieve, the time, personnel and economic investment of the certification and the choice of the scheme under which the certification will be carried out (it must be one of the countries included in the authorizing members).
Once these points have been clarified, it is feasible to start the process of drafting all the paperwork.
Requirements for Common Criteria.
The requirements needed to carry out a Common Criteria evaluation depend significantly on the EAL/PP the product will be facing. Although there are requirements common to all assurance levels and protection profiles, there are many other requirements that depend on the product's EAL/PP chosen. If you want to know more about the requirements requested for each EAL, check our Common Criteria cheat sheet
EAL or Protection Profile (PP)?
Both, Evaluation Assurance Level (EAL) and Protection Profile (PP), are guidelines that indicate the security requirements that the product must pass in order to obtain Common Criteria certification.
A PP specifies generic security evaluation criteria to substantiate vendors' claims of a given family of information system products and includes an EAL. An EAL is less specific as it does not refer to a specific type of product but to an assurance level.
Preferably and if possible, the product should be evaluated in conformance to a PP.
FIPS 140-3 Frequent Questions
Security requirements for FIPS 140-3
The areas covered, related to the secure design and implementation of a cryptographic module, include specification; ports and interfaces; roles, services, and authentication; finite state model; physical security; operational environment; cryptographic key management; electromagnetic interference/electromagnetic compatibility (EMI/EMC); self-tests; design assurance; and mitigation of other attacks.
Do I need a cryptographic module for a FIPS certification?
FIPS 140-3 is a standard developed by the NIST to define requirements to be satisfied by a cryptographic module. So, to achieve a FIPS certification, you will need a cryptographic module included in your product, otherwise it makes no sense.
How to determine FIPS compliance level?
There are four compliance levels from level 1 (lowest level) to level 4 (highest level):
Level 1: Very low requirements, involves production-grade equipment and externally tested algorithms.
Level 2: Adds requirements for physical tamper-evidence and role-based authentication. Software implementations must run on an Operating System approved to Common Criteria at EAL2.
Level 3: Hardware must feature physical tamper-resistance and identity-based authentication. There must also be physical or logical separation between the interfaces by which “critical security parameters” enter and leave the module. This level offers the best balance and compromise between effective security and operational convenience.
Level 4: This is the highest level, makes the physical security requirements more stringent, its main goal is to avoid environmental attacks, so requires much more robustness again these types of attacks.
FIPS compliant and approved algorithms.
There is a current list of FIPS validates algorithms, if your device is running an algorithm developed for a third party, check if is already validated by the NIST.
Otherwise, if you are developing your our algorithm and you want it to be approved by the NIST, you must pass a FIPS certification. Our advice is that, first of all, to contact a consultancy firm, as jtsec, before starting any further steps.
How many assurance levels are for FIPS 140-3?
There are four assurance level for FIPS 140-3, from 1 to 4. The standard provides four increasing qualitative levels of security, the higher the number, the higher the requirements to pass the evaluation. These levels are intended to cover the wide range of potential applications and environments in which cryptographic modules may be employed, the most common ones are levels 1 and 2.
ETSI EN 303 645 Frequent Questions
What is ETSI EN 303 645?
ETSI EN 303 645 is a European standard that outlines specific cybersecurity requirements for consumer IoT devices. It aims to ensure that these devices are designed, developed, and maintained with security in mind.
What does ETSI EN 303 645 cover?
ETSI EN 303 645 covers a wide range of cybersecurity requirements for consumer IoT devices. It includes aspects such as secure passwords, secure firmware updates, protection against unauthorized access, secure network connections, and encryption of personal data.
Who developed the ETSI EN 303 645 standard?
The ETSI EN 303 645 standard was developed by the European Telecommunications Standards Institute (ETSI), which is a recognized European standards organization for information and communications technologies.
Is compliance with ETSI EN 303 645 mandatory?
Compliance with ETSI EN 303 645 is not currently mandatory by law, but it is widely recognized and encouraged as a best practice for ensuring the cybersecurity of consumer IoT devices. Compliance may be required by certain industry organizations, certifications, or regulatory bodies.
What types of devices does ETSI EN 303 645 apply to?
ETSI EN 303 645 applies to a wide range of consumer IoT devices, including smart home devices, wearables, connected toys, healthcare devices, and other similar products. It covers devices that are intended for consumer use and are connected to the internet.
Are there different levels of compliance with ETSI EN 303 645?
ETSI EN 303 645 does not specify different levels of compliance. Instead, it outlines specific requirements that consumer IoT devices should meet. Compliance is typically assessed on a pass/fail basis for each requirement.
How can manufacturers demonstrate compliance with ETSI EN 303 645?
Manufacturers can demonstrate compliance with ETSI EN 303 645 by implementing the required cybersecurity measures and documenting their adherence to the standard. This may involve performing self-assessments, conducting security testing, and providing relevant documentation to show compliance.
Can ETSI EN 303 645 be used globally?
While ETSI EN 303 645 is a European standard, its principles and requirements can be applied globally. The standard provides valuable guidance for improving the cybersecurity of consumer IoT devices, regardless of the geographical location.
Does ETSI EN 303 645 address privacy requirements?
While ETSI EN 303 645 primarily focuses on cybersecurity, it does include some privacy-related requirements. For example, it addresses the protection of personal data, encryption of sensitive information, and secure management of user credentials.
Are there any other standards or regulations that ETSI EN 303 645 aligns with?
ETSI EN 303 645 aligns with other prominent cybersecurity standards and regulations, such as the General Data Protection Regulation (GDPR) in the European Union and the California Consumer Privacy Act (CCPA) in the United States. Compliance with ETSI EN 303 645 can help organizations meet the cybersecurity requirements of these regulations.
How frequently is ETSI EN 303 645 updated?
ETSI EN 303 645 may be periodically updated to reflect evolving cybersecurity threats and best practices. It is recommended to check for updates from ETSI to ensure compliance with the most recent version of the standard.
Is there any certification specifically for ETSI EN 303 645 compliance?
Currently, there is no specific certification for ETSI EN 303 645 compliance. Compliance is typically self-assessed by manufacturers or can be evaluated through third-party security assessments or audits.
Do the certifications include provisions for ongoing vulnerability management and patching?
Ongoing vulnerability management and patching are crucial for maintaining the security of IoT devices. Check if the certifications require the manufacturer to have processes in place for vulnerability monitoring, timely patching, and security updates.
Are there any specific privacy or data protection requirements addressed by this certification?
Privacy and data protection are integral to IoT security. Assess if the certifications address specific privacy or data protection requirements, such as data encryption, user consent mechanisms, anonymization techniques, or adherence to relevant data protection regulations.
How do the ETSI EN 303 645 certification align with regional or international data protection regulations (e.g., GDPR, CCPA)?
IoT devices should align with regional or international data protection regulations, such as GDPR (General Data Protection Regulation) or CCPA (California Consumer Privacy Act). Verify if the certifications incorporate requirements or principles aligned with these regulations to ensure compliance.
Can this certification be independently verified or cross-checked with the certification body?
Independent verification adds credibility to the certifications. Check if the certification can be verified directly with the issuing certification body. This allows you to confirm the authenticity and validity of the claimed certifications.
CPSTIC Frequent Questions
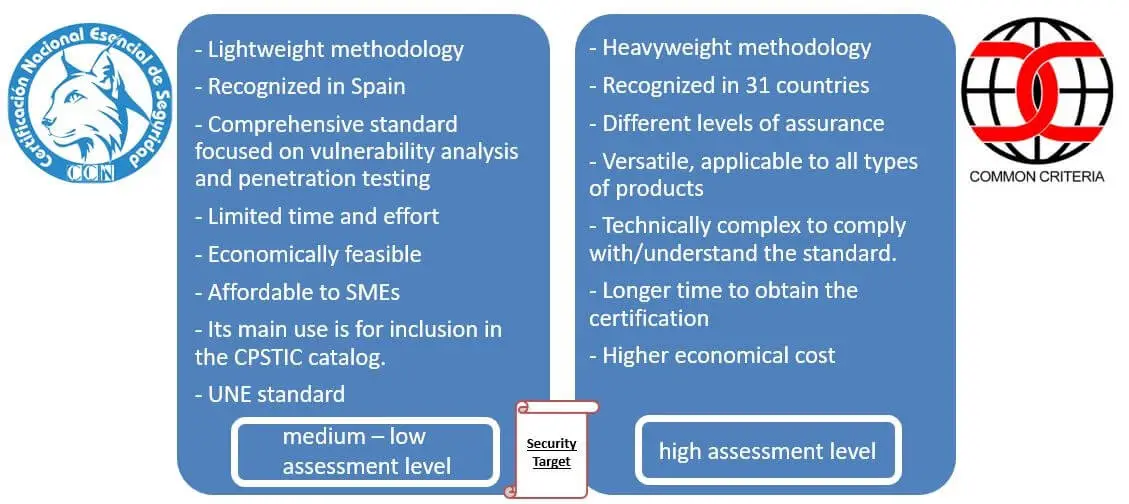
What cybersecurity certifications allow access to the CPSTIC catalogue?
There are only two certifications that allow a product to be included in the catalogue, LINCE y Common Criteria. We have to take into account that a product that obtains a Common Criteria certification may be required to undergo a series of complementary tests by the catalog to allow access to it, the so-called STIC complementary evaluations.
What is a STIC complementary evaluation?
It is a type of evaluation that is required for some products that have a Common Criteria certification and intend to enter the catalogue.It basically consists of complementing the original certification with functional tests and penetration tests.
The complementary STIC is required in case the scope of the original evaluation (declared in the Security Target) does not meet the RFS (Fundamental Security Requirements for its acronym in Spanish) determined for a certain taxonomy.
What kind of products are included in the CPSTIC catalog depending on the security level chosen?
The CPSTIC catalogue includes two types of products depending on the security level (high, medium or low) that the manufacturer wishes to achieve for its product:
- Approved products and services: They handle classified information, so the type of evaluation required to access the catalog is Common Criteria and the security level is high.
- Qualified products and services: These are products that have certified security functionalities and are suitable for use in systems affected by the ENS (Spanish national security scheme), in any of its categories (High, Medium and Basic). They are able to access by achieving a LINCE or Common Criteria certification.
If my product does not fit within the taxonomy offered by the CPSTIC catalogue, may I include it?
The catalogue is constantly evolving, so it gradually incorporates new families and categories if deemed appropriate. In this case, the fundamental security requirements of the product must be agreed with the catalogue and the Security Target must be created for approval.
In these cases, the catalogue can make two choices: create a taxonomy if it considers that there may be a significant number of similar products to be certified, or simply recommend their inclusion in the "Others" category.
At jtsec we have collaborated in the inclusion of several products that, due to their nature, could not be included in any of the existing categories.
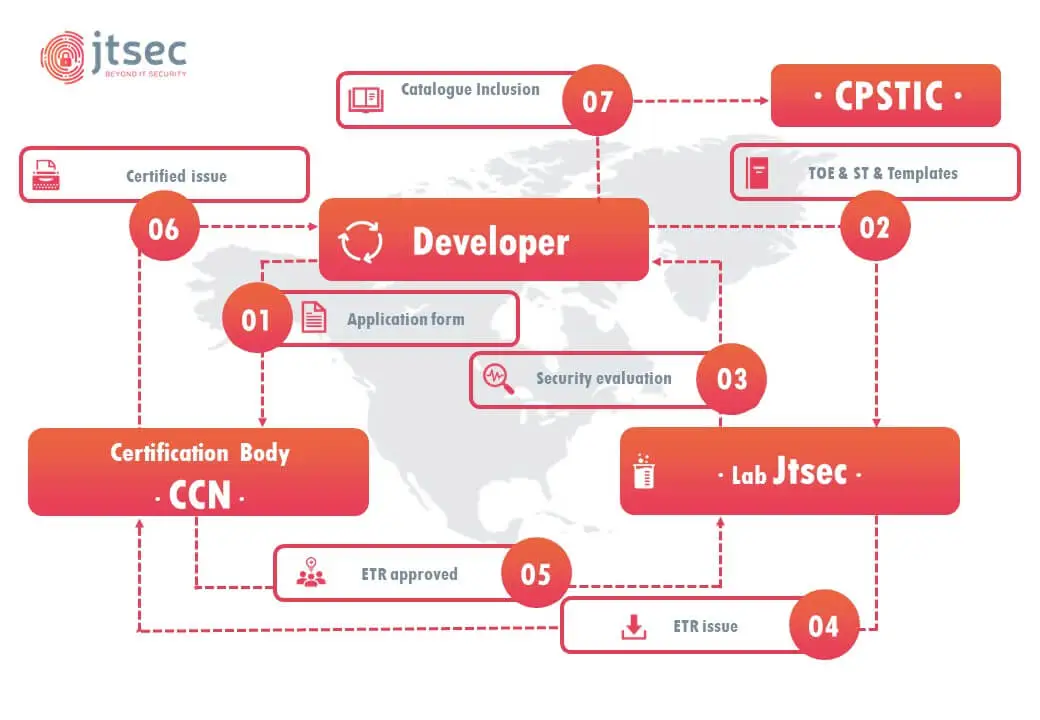
What process do I have to follow to include my product in the catalog?
The first step is to analyze your product and the internal resources of your company,as obtaining a certification requires considerable effort. The second step is to analyze what level of security you want to achieve and what market you want to cover. If your desire is to reach the high ENS security level and an international market, you have to pass a Common Criteria evaluation to access the catalog, otherwise it may be a better idea to pass a LINCE evaluation, which is more affordable in terms of cost and time, although its scope is limited to the Spanish market.
Once the decision has been made, the consulting part begins with the drafting of the Security Target and, in the case of Common Criteria, the rest of the required documentation. When the Security Target has been approved by the CPSTIC catalogue, the evaluation phase (laboratory) begins, where the product will be evaluated , including functional tests, vulnerability analysis and penetration tests.
At the end of the evaluation, the validation phase is initiated by the Certification Body. If the validation is satisfactory, the certificate is issued and the product is included in the CPSTIC catalogue.
How to keep the version of my product updated in the CPSTIC catalogue?
One of the main objectives of CCN is to keep the CPSTIC catalogue as up to date as possible for this, the most logical way is to speed up the qualification and inclusion of products in the catalog through the Continuous Qualification Process. To have a more accurate idea about this process, we recommend you to read the post we created specifically for this topic. dynamic process of updating versions allows manufacturers great flexibility so that their certified product does not become obsolete in the catalogue.
Does my product must be in the catalogue to be able to work with the Public Administration?
Actually it is NOT an essential requirement , although it is highly recommended. Everything points to the fact that, in the near future, taking into account the presence and importance that the catalog is taking and the number of cyber-attacks suffered by the Public Administration , the most logical thing is to prioritize the use of products that have passed a cybersecurity evaluation.
In addition, there has been an increase in the number of specifications, both from private companies and the public administration, which require applicants to offer products that are included in the catalog. This will be a great competitive advantage for those manufacturers who already have products in the catalogue.
Which cybersecurity laboratories can perform the evaluation tests?
CCN recognizes a number of accredited laboratories for both LINCE and Common Criteria evaluations. Only accredited laboratories have the competence to perform the relevant tests for either methodologies jtsec is accredited for both LINCE and Common Criteria by ENAC.
Is it mandatory to perform the Preliminary Report of Conformity of the Fundamental Security Requirements (RFS)?
It is not mandatory, but it is highly recommended to perform this report, as it saves time and avoids possible future problems once the process has started t allows to know in which stage the product is according to the catalogue regarding in terms of security. Suitable compliance with the Fundamental Security Requirements of the catalogue is important, but it is not absolutely essential to comply with all of them.
What happens if my product does not comply with a Fundamental Security Requirement of the taxonomy?
It is recommended to comply with all the Fundamental Security Requirements, however, several times, taxonomies do not perfectly match with all products.
In these cases. it is necessary to justify to CPSTIC that there are other measures that make that the non-compliance of this requirement does not affect the security of the product.
Is it possible to evaluate a cloud service?
Yes, as mentioned above, CCN is working hard to update and expand the CPSTIC catalog, that’s why it has added a new category to the taxonomy relating to cloud services. In fact, the first pilot projects are already ongoing.
IEC 62443 Frequent Questions
What is IEC 62443?
IEC 62443 is a series of international standards developed by the International Electrotechnical Commission (IEC) that focuses on industrial automation and control systems (IACS) cybersecurity.
What does IEC 62443 cover?
IEC 62443 covers a comprehensive set of cybersecurity requirements, guidelines, and practices specifically tailored for industrial control systems. It addresses aspects such as network security, access control, system hardening,security management, and secure development lifecycle.
How is IEC 62443 different from other cybersecurity standards?
Unlike general-purpose cybersecurity standards, IEC 62443 specifically addresses the unique challenges and requirements of industrial control systems. It takes into account the critical nature of these systems and the potential impact of cyber threats on safety, availability, and reliability.
What are the different parts of the IEC 62443 series?
The IEC 62443 series consists of multiple parts, each focusing on different aspects of IACS cybersecurity. These parts include concepts and models, risk assessment, system design, system implementation, operation, and maintenance, and security capabilities of system components.
Who should use IEC 62443?
IEC 62443 is intended for use by various stakeholders involved in the design, implementation, operation, and maintenance of industrial control systems. This includes system integrators, equipment manufacturers, asset owners, and cybersecurity professionals working in industrial environments.
Is compliance with IEC 62443 mandatory?
Compliance with IEC 62443 is not mandatory by law, but it is highly recommended and widely adopted within industries that rely on industrial control systems. Compliance with the standard demonstrates a commitment to cybersecurity and helps mitigate the risks associated with cyber threats.
Can organizations become certified for compliance with IEC 62443?
Yes, organizations can undergo certification processes to demonstrate compliance with IEC 62443. Certification is typically performed by third-party organizations authorized by the IEC. It involves an assessment of an organization's cybersecurity practices and their alignment with the requirements of the standard.
Are there different levels of compliance within the IEC 62443 framework?
The IEC 62443 framework defines different security levels, ranging from SL1 (basic) to SL4 (highly secure). These security levels help organizations determine the appropriate level of security measures required based on the risk assessment of their industrial control systems.
How can organizations implement the security measures outlined in IEC 62443?
Implementing the security measures outlined in IEC 62443 involves a systematic approach that includes risk assessment, system design, implementation, operation, and maintenance. Organizations can start by conducting a thorough assessment of their industrial control systems to identify vulnerabilities and potential risks. Based on the assessment, they can then design and implement appropriate security controls, such as network segmentation, access control mechanisms, intrusion detection systems, and incident response plans. Regular monitoring, maintenance, and updates are also essential to ensure ongoing security and compliance with the standard.
Does IEC 62443 address the issue of legacy systems?
Yes, IEC 62443 recognizes the presence of legacy systems in industrial environments and provides guidance on how to address their cybersecurity challenges. It offers strategies for securing legacy systems, such as implementing compensating controls, isolation measures, and regular patching and updates where applicable. The standard emphasizes the importance of risk assessment and the need to balance security requirements with the operational limitations of legacy systems.
Is IEC 62443 applicable to specific industries or sectors?
IEC 62443 is applicable to a wide range of industries and sectors that utilize industrial control systems. This includes sectors such as manufacturing, energy and utilities, transportation, critical infrastructure, and more.
How can organizations implement IEC 62443?
Implementing IEC 62443 involves conducting a thorough risk assessment, applying security controls, implementing secure network architectures, conducting security awareness training, establishing incident response plans, and regularly monitoring and maintaining the security of industrial control systems.
Does IEC 62443 address physical security of industrial control systems?
Yes, IEC 62443 recognizes the importance of physical security for industrial control systems. It includes requirements and recommendations for physical access controls, video surveillance, environmental protections, and other measures to safeguard the physical infrastructure of IACS.
Does IEC 62443 address the secure development of industrial control system software?
Yes, IEC 62443 includes guidelines and requirements for the secure development of software used in industrial control systems. It covers secure coding practices, software verification and validation, and vulnerability management throughout the software development lifecycle.
Is IEC 62443 applicable to legacy industrial control systems?
Yes, IEC 62443 can be applied to both new and existing industrial control systems, including legacy systems. The standard provides guidance on how to assess and improve the cybersecurity of legacy systems over time.
Is IEC 62443 aligned with other cybersecurity standards and regulations?
Yes, IEC 62443 aligns with other cybersecurity standards and regulations, such as ISO 27001 and NIST Cybersecurity Framework. It also takes into account regional regulations and requirements specific to industrial control systems.
How frequently is IEC 62443 updated?
IEC 62443 is regularly updated to keep pace with evolving cybersecurity threats and best practices. It is important to stay informed about updates to ensure ongoing compliance with the latest version of the standard.
Where can I find more information about IEC 62443?
More information about IEC 62443 can be obtained from the IEC website, which provides access to the standard documents, publications, and related resources. Additionally, consulting firms and cybersecurity professionals with expertise in industrial control systems can provide guidance and assistance in implementing IEC 62443 requirements.
IEC 62443-1 Frequent Questions
What is IEC 62443-4-1?
IEC 62443-4-1 is a specific part of the IEC 62443 series that focuses on the technical security requirements for industrial automation and control systems (IACS). It provides guidance on the secure product development lifecycle for IACS components.
What does IEC 62443-4-1 cover?
IEC 62443-4-1 covers the security requirements and recommendations for the secure development of IACS components. It addresses topics such as security management, security by design principles, security testing, secure coding practices, and vulnerability management.
Who should use IEC 62443-4-1?
IEC 62443-4-1 is intended for use by manufacturers, system integrators, and developers involved in the design and development of IACS components. It provides guidance on implementing security measures throughout the product development lifecycle.
How does IEC 62443-4-1 relate to other parts of the IEC 62443 series?
IEC 62443-4-1 is part of the broader IEC 62443 series on industrial control system cybersecurity. It specifically focuses on the secure development of IACS components, complementing other parts of the series that address different aspects of IACS security.
What are the key requirements for secure product development according to IEC62443-4-1?
The key requirements for secure product development outlined in IEC 62443-4-1 include incorporating security into the development process, performing security risk assessments, implementing secure coding practices, conducting security testing, and ensuring secure configuration and deployment of the components.
Does compliance with IEC 62443-4-1 require certification?
Compliance with IEC 62443-4-1 does not require specific certification. However, organizations may choose to undergo third-party audits or assessments to demonstrate compliance with the standard and gain credibility.
Can IEC 62443-4-1 be applied to both hardware and software components?
Yes, IEC 62443-4-1 is applicable to both hardware and software components of industrial control systems. It provides guidance on securing the design, development, and testing processes for both hardware and software elements.
How does IEC 62443-4-1 address secure coding practices?
IEC 62443-4-1 provides guidelines for secure coding practices, including the use of secure coding standards, vulnerability testing, and code review processes. It promotes the adoption of coding practices that minimize security vulnerabilities in IACS components.
Does IEC 62443-4-1 cover security testing and vulnerability management?
Yes, IEC 62443-4-1 addresses security testing and vulnerability management as part of the secure product development lifecycle. It emphasizes the importance of conducting security testing, including penetration testing and vulnerability assessments, and implementing a robust vulnerability management process.
How does IEC 62443-4-1 address security documentation and traceability?
IEC 62443-4-1 emphasizes the need for comprehensive security documentation throughout the product development lifecycle. This includes documentation related to security requirements, risk assessments, design decisions, security testing results, and traceability of security-related activities.
Is IEC 62443-4-1 applicable to legacy components?
Yes, IEC 62443-4-1 can be applied to both new and existing IACS components, including legacy components. It provides guidance on assessing the security of legacy components and implementing necessary security measures to mitigate risks.
How often is IEC 62443-4-1 updated?
IEC standards, including IEC 62443-4-1, are periodically updated to address emerging cybersecurity threats and incorporate industry best practices. It is important to stay informed about updates and revisions to ensure compliance with the latest version of the standard.
Are there any certification programs related to IEC 62443-4-1?
While IEC 62443-4-1 itself does not have specific certification programs, some certification bodies may offer certifications related to the secure development of IACS components. These certifications can provide validation of an organization's adherence to IEC 62443-4-1 and demonstrate their commitment to secure product development practices.
Can IEC 62443-4-1 be used in combination with other cybersecurity standards?
Yes, IEC 62443-4-1 can be used in combination with other cybersecurity standards and frameworks to enhance the overall cybersecurity posture of IACS components. It can be aligned with industry-specific standards, regional regulations, and international frameworks such as ISO 27001 or NIST Cybersecurity Framework.
Where can I find more information about IEC 62443-4-1?
More information about IEC 62443-4-1 can be obtained from the IEC website, which provides access to the standard document itself, as well as additional resources and guidance
IEC 62443-2 Frequent Questions
What is IEC 62443-4-2?
IEC 62443-4-2 is a specific part of the IEC 62443 series that focuses on the technical security requirements for system integration of industrial automation and control systems (IACS).
What does IEC 62443-4-2 cover?
IEC 62443-4-2 covers the security requirements and recommendations for the system integration process of IACS. It addresses topics such as secure network architecture, secure configuration of network components, secure communication, and segregation of networks.
Who should use IEC 62443-4-2?
IEC 62443-4-2 is intended for use by system integrators, engineering firms, and organizations involved in the integration of industrial automation and control systems. It provides guidance on implementing security measures during the system integration process.
How does IEC 62443-4-2 relate to other parts of the IEC 62443 series?
IEC 62443-4-2 is part of the broader IEC 62443 series on industrial control system cybersecurity. It specifically focuses on the security requirements and recommendations for system integration, complementing other parts of the series that address different aspects of IACS security.
What are the key security requirements for system integration according to IEC 62443-4-2?
The key security requirements for system integration outlined in IEC 62443-4-2 include the development of a security plan, implementation of secure network architecture, secure configuration of network components, secure communication protocols, and appropriate segregation of networks.
Does compliance with IEC 62443-4-2 require certification?
Compliance with IEC 62443-4-2 does not require specific certification. However, organizations may choose to undergo third-party audits or assessments to demonstrate compliance with the standard and gain credibility.
Can IEC 62443-4-2 be applied to both new and existing industrial controlsystems?
Yes, IEC 62443-4-2 can be applied to both new and existing industrial control systems. It provides guidance on implementing security measures during the system integration process, regardless of the age or stage of the system.
How does IEC 62443-4-2 address secure network architecture?
IEC 62443-4-2 provides guidelines for designing and implementing a secure network architecture for industrial control systems. It covers aspects such as network segmentation, access control, intrusion detection, and secure configuration of network devices.
Does IEC 62443-4-2 address secure communication between system components?
Yes, IEC 62443-4-2 addresses the security requirements for communication between system components within an industrial control system. It emphasizes the use of secure communication protocols, encryption, and authentication mechanisms to protect the integrity and confidentiality of data.
How does IEC 62443-4-2 address the segregation of networks?
IEC 62443-4-2 provides guidance on the appropriate segregation of networks within an industrial control system. It outlines the principles and practices for separating networks based on security zones and implementing access control measures to prevent unauthorized access between zones.
Is IEC 62443-4-2 applicable to cloud-based or remote access systems?
Yes, IEC 62443-4-2 can be applied to cloud-based or remote access systems within the context of industrial control systems. It provides recommendations for ensuring the security of such systems, including secure authentication, encryption, and secure communication protocols.
How often is IEC 62443-4-2 updated?
IEC standards, including IEC 62443-4-2, are periodically updated to address emerging cybersecurity threats and incorporate industry best practices. It is important to stay informed about updates and revisions to ensure compliance with the latest version of the standard.
Are there any certification programs related to IEC 62443-4-2?
While IEC 62443-4-2 itself does not have specific certification programs, some certification bodies may offer certifications related to the secure system integration of industrial control systems. These certifications can provide validation of an organization's adherence to IEC 62443-4-2 and demonstrate their commitment to secure integration practices.
Can IEC 62443-4-2 be used in combination with other cybersecurity standards?
Yes, IEC 62443-4-2 can be used in combination with other cybersecurity standards and frameworks to enhance the overall cybersecurity posture of industrial control systems. It can be aligned with industry-specific standards, regional regulations, and international frameworks such as ISO 27001 or NIST Cybersecurity Framework.
Where can I find more information about IEC 62443-4-2?
More information about IEC 62443-4-2 can be obtained from the IEC website, which provides access to the standard document itself, as well as additional resources and guidance.

