What is FIPS 140-2
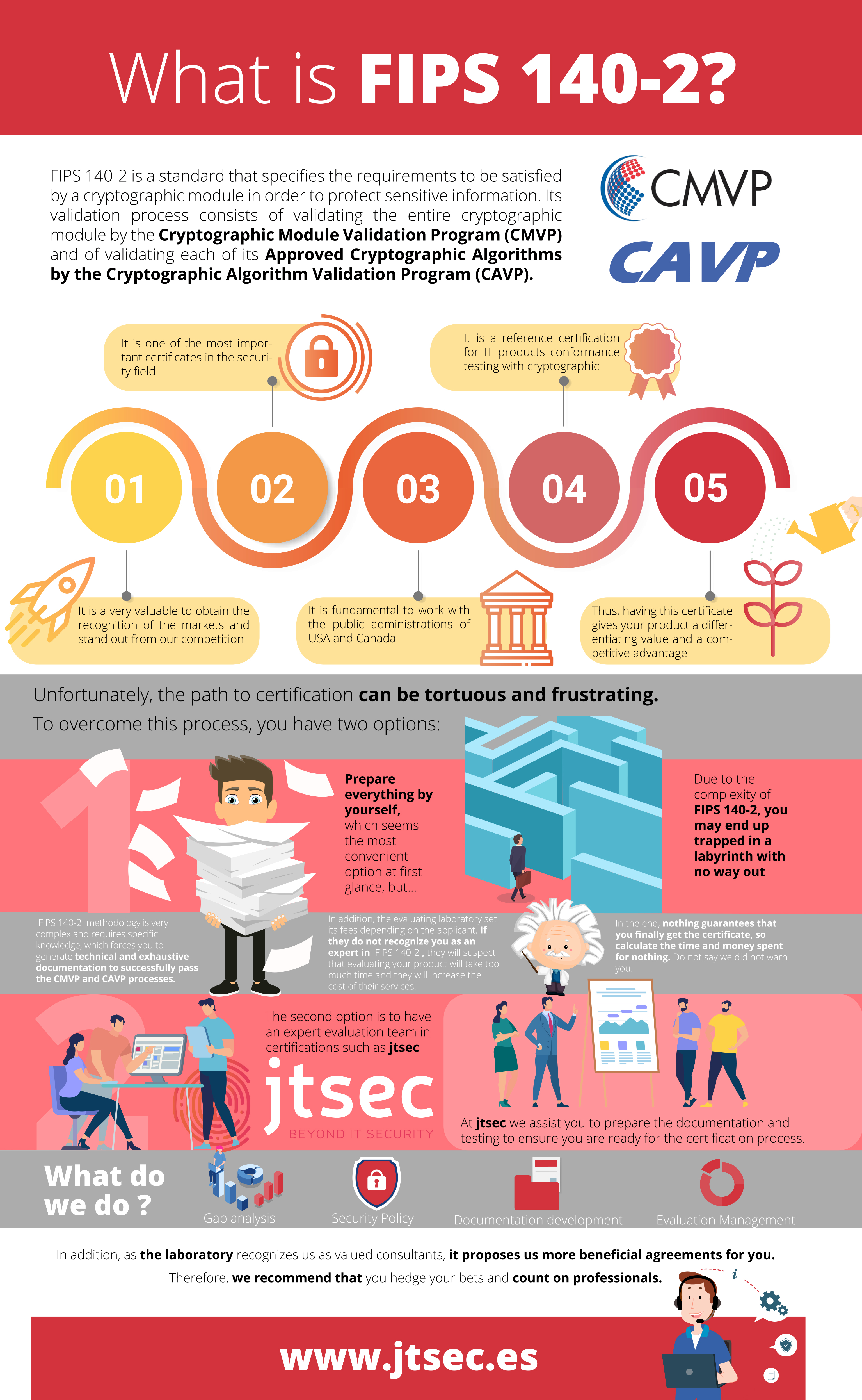
FIPS 140-2 is a standard developed by the National Institute of Standards and Technology (NIST) and Communications Security Establishment Canada (CSEC) to define the requirements to be satisfied by a cryptographic module in order to protect sensitive information. It is one of the most important certificates in the security field related to the cryptography that will give a competitive advantage to your product.


This standard is needed for validating the cryptographic modules used by the Federal Agencies (US and Canadian governments) considering as cryptographic module any hardware, software or firmware able to provide cryptographic algorithms contained in the Approved Security Functions defined by the NIST and CSEC.



The standard defines four increasing level of security (SL1, SL2, SL3 and SL4) which cover the 11 areas related to the design and implementation of a cryptographic module.
Generally, vendors must generate the documentation to be submitted to the Cryptographic and Security Testing (CST) laboratories to comply with FIPS 140-2 requirements based on the FIPS 140-2 Derived Test Requirements (DTR) and the Implementation Guidance (IG). Therefore, if the company has not adopted a security certification culture feel overwhelmed by the prospect of needing to generate a huge amount of documentation to pass the validation, as well as to make unexpected or drastic changes in their products.
In our experience, the doubts experimented by the manufacturers in the most cases, result in long delays in the module development and certification, even making it impossible in some cases.
Do not wait and call us to get more information about FIPS 140-2 consulting, our expert evaluation team will assist you to get your module successfully validated.
FIPS 140-2 Validation Process
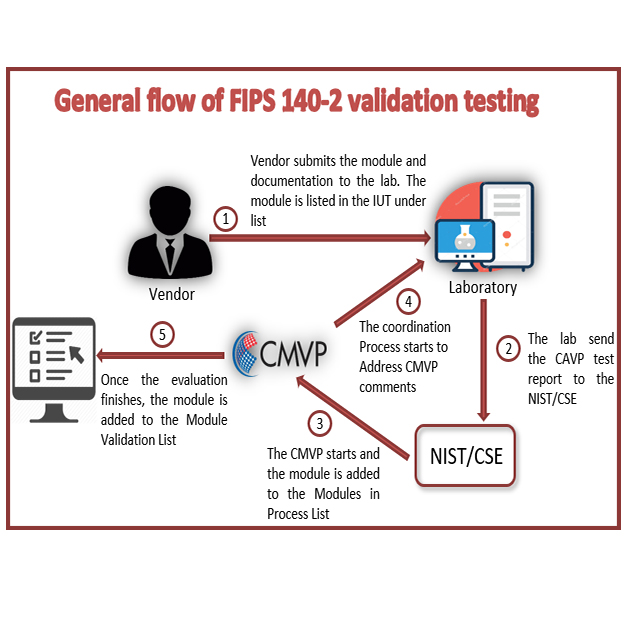
Firstly, the validation process consists of the validation of the Approved Cryptographic algorithms by the CST laboratory based on the Cryptographic Algorithm Validation Program (CAVP) using a series of tests to verify the correct cryptographic functionality. Secondly, once the CAVP is passed, the entire cryptographic module is validated by the Cryptographic Module Validation Program (CMVP).
The FIPS 140-2 validation process involves mainly the vendor and the CST lab. NIST and CSEC are involved to review the reports submitted by the CST lab to ensure that the CAVP has been passed successfully and that the documentation and module design comply with the standard.
The first step is to get the module listed in the “Cryptographic Module Validation Program FIPS 140-2 Implementation Under Test List which shows the IUT that are being tested by a CST lab. To get the module included in this list, the vendor must send the documentation package to the CST lab.
Once the testing process has been finished by the CST, the module is listed in the “Cryptographic Module Validation Program FIPS 140-2 Modules in Process List” waiting for the documentation to be reviewed by the NIST/CSEC.
Finally, the IUT will be listed in the “FIPS 140-2 Cryptographic Module Validation Lists” as soon as the validation finishes with success.
After a preliminary GAP analysis, our team can accompanies you during the whole process of designing the module, starting by identifying the level of security that it must comply with, which of its parts belong within the boundary, what services it must offer and what states the finite state model have in accordance to the cryptographic operations that are to be implemented. In addition, we will write the entire documentation package composed by the Security Policy, Finite State Model, Functional Specification and Configuration Item List.
Ask us about our FIPS 140-2 consulting service and get your product on the list now reducing the time of validation and getting a better beneficial for you based on our experience and our recognition as valued consultants for laboratories.
They already trusted us. Let's talk!
What we offer?
Gap Analysis
We check the current status of your product and documentation informing you about the changes you need to carry out before going through the development/certification process.
This service is quite interesting in FIPS 140-2 given that Cryptographic Modules must meet some specific requirements and having a clear understanding of them, avoid to find issues at the last stages of the development.
Consultancy
If you need your Cryptographic module to become a validated FIPS 140-2 CM; we can offer you the maximum support during the process to get it.
Writing a Security Policy or a Finite State Machine is not a trivial task if you are not used to.
We can do it for you allowing you to focus on your product and saving your time and money.
Training
Does your team need to gain more knowledge in FIPS 140-2? We can provide you a customized training.
After this training, your team will be able to write FIPS 140-2 documentation on their own.