The Continuous Qualification Strategy mainly concerns those manufacturers and/or developers who already have a product in the Catalogue and whose version has become obsolete due to the development of later versions and wish to include them in the catalogue.
What is the Continuous Qualification Strategy and how does it affect already certified products?
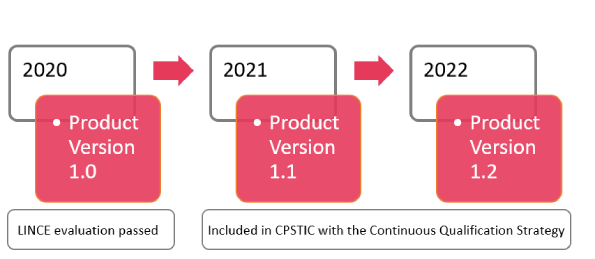
Nowadays, manufacturers are continuously developing and improving their products. Therefore, at the time of obtaining a certification (a process that can take several months), the product already has versions that are later than the certified one, thus creating a mismatch between the versions that the manufacturer is developing and the version that appears in the catalogue.
To solve this type of mismatch, CCN created the Continuous Qualification Strategy, to keep the CPSTIC, CCN-STIC 105 catalogue as up to date as possible, thus speeding up the qualification and inclusion of products in the catalogue. This process consists of of evaluating software versions, firmware or hardware models not included in the initial certification without the need to carry out a complete evaluation process.
It is an open-ended process in which new versions of the product are analysed. In case the changes do not affect the security of the product, the Differential Analysis Report (IAD by its acronym in Spanish) is written justifying that testing of the new version of the product is not necessary. If the changes affect security, a complementary STIC assessment is performed on the affected security functionality.
This applies to a large number of manufacturers who create different versions of the same product whose differences are minimal with respect to the already certified product.
When does Continuous Qualification apply?
There are several compelling reasons why a manufacturer may wish to apply Continuous Qualification to their product.
Continuous Qualification will apply in the following cases:
CrowdStrike success case, Continuous Qualification process from the manufacturer´s point of view.
CrowdStrike is an American cybersecurity technology company based in Austin, Texas. Its products are based on protecting the most critical areas of enterprise risk - endpoints and cloud workloads, identity and data - to keep customers ahead of today´s adversaries and stop breaches.
They currently have one product listed in the CPSTIC / CCN STIC - 105 catalogue Falcon Sensor v.6.27.14102. However, due to the fast evolution of the product, that version soon became obsolete, so they decided to apply Continuous Qualification to list the latest available version, Falcon Sensor v.6.40, in the catalogue
The process comprised conducting a Security Requirements Impact Analysis (Updated IAD) with the changes that had been made between both versions and checking that the new version did not contain modifications that affected compliance with the security requirements included in the LINCE certification, so no additional tests had to be performed to verify the viability of the new version to enter the catalogue. From jtsec we congratulate CrowdStrike for the inclusion of the new version of its Falcon Sensor product and thank them for their confidence in us.
CrowdStrike is a pioneer company at national level with the application of the strategy of continuous qualification, ensuring its customers that they can use the latest technology developed by the company securely.
❝Offering our customers maximum security in our products is key to continue generating confidence. That´s why we decided to include the latest version of our flagship product, the Falcon Sensor, in the reference cybersecurity catalogue for companies and public administrations. Thanks to jtsec, a laboratory that has already helped us to obtain LINCE certification, this process has been quite easy for CrowdStrikeAntonio Cortés, Public Sector Manager at CrowdStrike