The IEC 62443 standard is the main international reference framework for the cybersecurity of industrial systems and specifies a series of measures against cyber-attacks. It also provides a lingua franca for the industrial ecosystem (manufacturers, integrators and test laboratories). Is the only reliable solution for testing the cybersecurity of components in the field of industrial automation.
International standards are based on industry best practices and are reached by consensus. The implementation of IEC 62443 can mitigate the effects of cyber-attacks and often prevent them, strengthening security throughout the lifecycle and reducing costs. The main objective of this standard is to simplify trade between participating countries and increase the compatibility of international standards. This methodology provides, among other, these advantages:Main differences between IEC 62443 4-1 and IEC 62443 4-2
Which actors are part in the evaluation process?
The certification process is not simple and can take several months of effort to be completed. For this reason, we recommend using a reputable laboratory. The workload is also considerable for the client, since, mainly in the first part, the client has to justify the requirements it complies with for each standard and how it meets them.
There are three main actors involved in this process:
Flowchart of the Certification Process.
In this section we will highlight the most important stages in the certification process. With this graphic, the steps to be followed will become clearer. At the top we find the functions that depend on the company that applies and at the bottom those that depend on the laboratory or NCB/CB. As we can see, many of the activities depends on the client: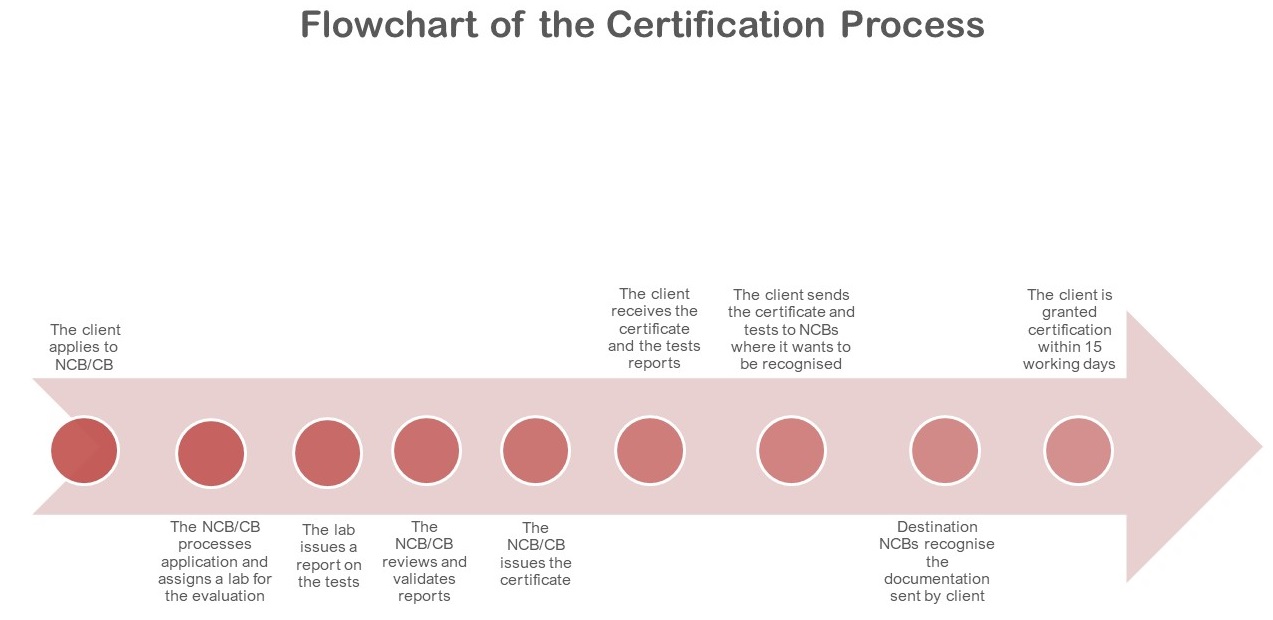
Important documentation required in the process.
There are some documents required to be carried out by the client, some others by the lab and just one by the CB/NCB.
At the beginning of the process, the client must declare at which level of maturity (4-1) or security level (4-2) want to assess the product. After that the client must write a Conformity Statement, which is a description of how the requirements are fulfilled. Once the evaluation is done, the lab fills the TRF (Test Report Form) with the information provided by the customer. The TRF is the output of the evaluation process and it will be submitted to the NCB. The NCB / CB is the body in charge of issuing the certificate.How can we help you achieving IEC 62443 4-1 & IEC 62443 4-2?
We strive to smooth the process and make it as simple as possible, minimizing the workload for our clients, as well we can highlight:
If you want more info do not hesitate to contact us.