On last May 12, a worldwide cyber-attack based on WannaCrypt ransomware software was carried out by cyber criminals, affecting a great number of important corporations in many countries. This event quickly appeared in every newspaper, news webpage, and social media. While rumors about important companies being attacked and forced to stop their services quickly spread among Internet news pages and social media, the number of countries and organizations attacked increased. Uncertainty at some degree of fear settled in the public opinion, who read about hackers kidnapping important information for world top companies.
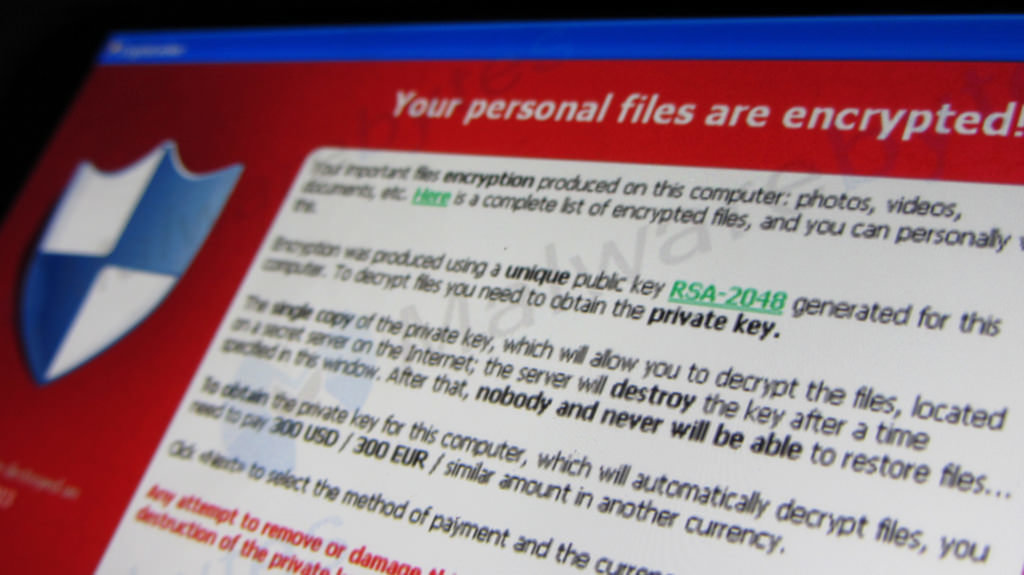
Later on that day, more information about technical details on the attack was provided. The software that spread through the companies computers was a kind of ransomware called WannaCrypt. Ransomware is a type of malicious software that ciphers files in the victim hard disk, rendering them unusable. Then the ransomware asks the victim for a payment, usually in bitcoins, in order to provide the key to decipher the files. Even it sets a deadline and if the payment is not done after a few days, the deciphering key will never be provided.
As a result, owners of the kidnapped information in the affected computers could be potentially forced to pay in order to recover the data. As most of the targeted computers belonged to important companies, such information was presumed to be critical and its loss could affect relevant services, clients or business secrets.
The question that was on everyone’s mind was how it could happen. World top companies are supposed to make huge investments in cyber-security and, suddenly, they had been attacked and their information was in danger. An important detail is that all the affected computers were running Windows operating system. A few hours later Microsoft published an article where they explained all the details of the recent attack.
In summary, the malicious software was introduced in the computers using social engineering ane e-mail phishing attack (emails that look from a legit sender but they contain an attachment or link to download malware). Once the malware was on the computers of the phished users, it propagated through the network by exploiting a vulnerability ( CVE-2017-0145) of that affected Windows systems earlier than Windows 10.
The funny part of the story is that Microsoft had already released a security update that fixed that vulnerability. The release date was on March 14, almost two months before. At this point, Microsoft blamed the IT administrators for not updating their systems, while IT admins claimed that installing updates on important systems require a big amount of tests before they can be deployed to production software.
Once this point was reached, one may wonder who was right. It may seem that two months seems a reasonable amount of time to perform tests and deploy critical security patches to production systems. Later, on social media, some relevant IT personalities of the affected companies claimed that they could recover the information using data backups previous to the attack, and everything was back to normal. However, they could not deny the operation downtime and the worldwide panic that happened.
If you are reading this article and you are related to a business or company that relies on information stored in IT systems, you could wonder if this could happen to you. You might be concerned and probably you should. The attack was stopped to a certain degree and everyone started patching their systems on that weekend but, since then, hundreds of news about new evolved forms of WannaCrypt come out day by day. If you are an owner, manager, or IT administrator of a company that holds important information on IT systems, you probably are asking yourself what you can do to prevent your data being kidnapped, or even stolen.
Anyway, if world top companies could not defend of WannaCrypt cyber-attack, how could a medium or small company do it? The answer is simple. If your company is small, it is easier to build cyber defenses, it requires less effort, and they will be more effective against threats.
The protection against cyber-attacks and other IT threats start by adopting a set of good IT practices. Some ISO norms exist, as catalogs of good practices, security measures, procedures among others. One of the most popular ISO norms and probably one of the most effective regarding IT security is ISO/IEC 27001.
ISO/IEC 27001 defines the concept of ISMS: Information Security Management System, a model to establish, implement, opérate, monitor, review, maintain and enhance the protection of the information assets in order to achieve the business objectives. An ISMS helps to establish policies, procedures, and controls regarding the company objectives.
Implanting ISO/IEC 27001 in a business comprises various phases. In the earlier stages, an inventory of information asset is elaborated, threats and vulnerabilities to the security of the information identified, as well as their impact, and risks are analyzed and evaluated. This is highly relevant to security, as we get to know what is to be attacked, how, and what would be the impact. Also, a measurement of probabilities and costs of those incidents is elaborated.
In the earlier stages, also an Information Security Policy is elaborated. This is a high-level document that states the security objectives of the information in the organization and explains the business and contractual requirements regarding information security. Besides, a series of other policies are written, targeting more specific aspects of security. Some of the most relevant are:
- Access control policy
- Cryptography policy
- Incident management policy
- Secure elimination and destruction policy
- Clean desktop and screen policy
- Backup policy
- Information transfer policy
- Security policy for relationships with providers
- Teleworking policy
- And others, according to the business needs and objectives
Those policies cover the most important aspects of security at a high level. Moreover, most of them are supported by technical specific documents named procedures. Procedure documents provide specific technical instructions to accomplish a task mentioned in a specific policy. For instance, the backup policy usually is accompanied by a procedure for backups, where it is explained in detail how the information backups are performed.
Besides, ISO/IEC 27001 defines a catalog of security controls, covering specific aspects of information security. The catalog is huge and has a control for almost anything that can be imagined regarding information security. Some of the topics covered by these controls are:
- Management direction for information security
- Internal organization of information security
- Mobile devices and teleworking
- Human resource security, prior, during and after employment
- Responsibility for assets
- Information classification
- Media handling
- Business requirement for access control
- User access management
- User responsibilities
- System and application access control
- Cryptographic controls
- Secure areas
- Equipment
- Operational procedures and responsibilities
- Protection from malware
- Malware
- Logging and monitoring
- Control of operational software
- Technical vulnerability management
- Information systems audit considerations
- Network security management
- Information transfer
- Security requirements of information systems
- Security in development and support processes
- Information security in supplier relationships
- Supplier service delivery management
- Management of information security incidents and improvements
- Information security continuity
- Redundancies
- Compliance with legal and contractual requirements
- Information security reviews
Each of those topics includes detailed technical controls, so the list is huge.
The different policies included in the ISMS as required by ISO/IEC 27001, along with their procedures, provide a detailed set of instructions to handle the most relevant the security aspects of the Information security in a Company, and they must make sure that the ISMS accomplishes the security controls of the ISO/IEC 27001 norm.
In summary, the implantation of ISO/IEC 27001 makes the business to adopt a set of security policies and procedures that ensure that the catalog of security controls of the norm are accomplished. This leaves the information systems of the company in an excellent security state, and they will be protected against most of the security threats that can comprise information. To this extent, a document named Statement of Applicability is elaborated, where it is stated how each control is implemented.
An ISO/IEC 27001 implantation has more stages that we won’t explain in this article. However, an important point that has to be mentioned is that it introduces a continual review process. Whenever the information systems change or an incident occurs, the ISMS is reviewed and, if needed, redesign and enhancements are performed to ensure everything is always up to date and the ISMS can answer to every possible threat.
If we think in the WannaCrypt ransomware event, and we situate it in the scenario of a Company where an ISO/IEC 27001 has been implanted, we can illustrate how it could help to mitigate the ransomware threat.
First, let’s see if we could have avoided the downloading of the malware. The way the ransomware entered the IT systems was mostly through phishing emails. In an ISO/IEC 27001 scenario, there are specific security controls, that requires a network management to protect information and security systems. According to this, the first fence could be a firewall that wouldn’t allow connecting with an email provider different than the corporative one, so if phishing mail was downloaded through personal e-mail accounts, the threat would have been stopped there.
If we assume the phishing email was opened in a corporate e-mail account, various circumstances could happen to prevent the download of the malware. First, our security policy for relationships with providers would have enforced choosing an e-mail provider that has a good phishing filter and would have blocked the e-mail. Secondly, our firewall would have blocked the e-mail itself or the download of the malware, or it could have rules that have denied the user to open the website hosting the malware, or blocked its download. So it would have never downloaded in the user computers.
Let’s imagine that somehow, the malware is downloaded. Multiple scenarios can be foreseen here. First, the user has to execute the downloaded malware. Let’s say it doesn’t require administration permissions. If it does, it would be blocked since users would have the minimum required privileges for their job, according to the access control policy. So, if the user tries to launch the executable, the Access control policy may still implement a system to allow the users to run only known programs. Therefore, the execution would be blocked as well. Finally, the IT security policies would state that the antivirus must be up to date and the latest system patches must be applied within a reasonable deadline. Considering the attack happened 2 months after Microsoft released the security patch, we could assume the OS patches and the antivirus would be up to date and the execution would have been blocked, or the associated vulnerability could not have been exploited.
If previous controls failed, we know the malware spread through the network due to a vulnerability in outdated operating systems. The spreading could have been stopped according to the controls of ISO/IEC 27001 that requires that the networks are segregated. So, it would have affected only a portion of the system, the ones connected to the network where the user downloaded the information, and not computers in other networks, for instance, belonging to other departments.
Even then, if the user has the mínimum privileges to access the information he requires for his job duties, the malware would have had privileges to cipher only a part of the information.
If the malware would have broken the many fences before ciphering information, and some of the documents would have been ciphered, the backup policy of the ISMS would have established a backup systems that would let us recover this information, performing frequent backups, and locating them in a place isolated from the computers that are backed up. So, in this unlikely scenario, we could still recover the information, without needing to pay the ransom.
Finally, the incident management procedures and continuous reviews of the ISO/IEC 27001 would make necessary to analyze what happened, and modify the ISMS to avoid the same happening in the future. There is also a control that ensures the IT staff of the organization is in touch with relevant security groups and forums, helping them in learning how to avoid these threats and implementing preventive security measures.
As seen in this article, the implantation of ISO/IEC 27001 provides a high level of IT security that helps avoiding and mitigating most of the threats that can affect information assets of a Company. Having it implanted in your company would ensure your information is safe and protected against most of the attacks. Even if some of your ISMS security measures are avoided, there will be additional defenses and, in the worst case scenario, ways to recover your information and ensure business continuity.
In jtsec we can help you with the implantation and auditory of ISO/IEC 27001 in your Company. Contact us if you’re interested